Photos courtesy of IBM
The classic story of the Trojan horse has long been used to show that objects aren’t always as they appear. After successfully defending against a siege by the Greek army, the story says that residents of the city of Troy took a large wooden horse statue left behind by the retreating Greeks, and put it on display within the city walls. However, the statue actually contained Greek spies who crept out under cover of darkness and sabotaged the city’s defenses from the inside.
In the computing world, the term Trojan horse has come to represent ordinary-looking software that masks a hidden payload of malware. However, there are other ways that cybercriminals are employing this covert methodology to break through defenses. Specifically, hackers are now sending packages that contain concealed hardware devices that allow them to break into secure facilities from within. This technique has become known as warshipping.
Charles Henderson is the Global Head of IBM’s X-Force Red, a team of veteran hackers who analyze digital security vulnerabilities and advise companies on how to defend against them. He recently wrote a blog article for SecurityIntelligence explaining the rise of warshipping.
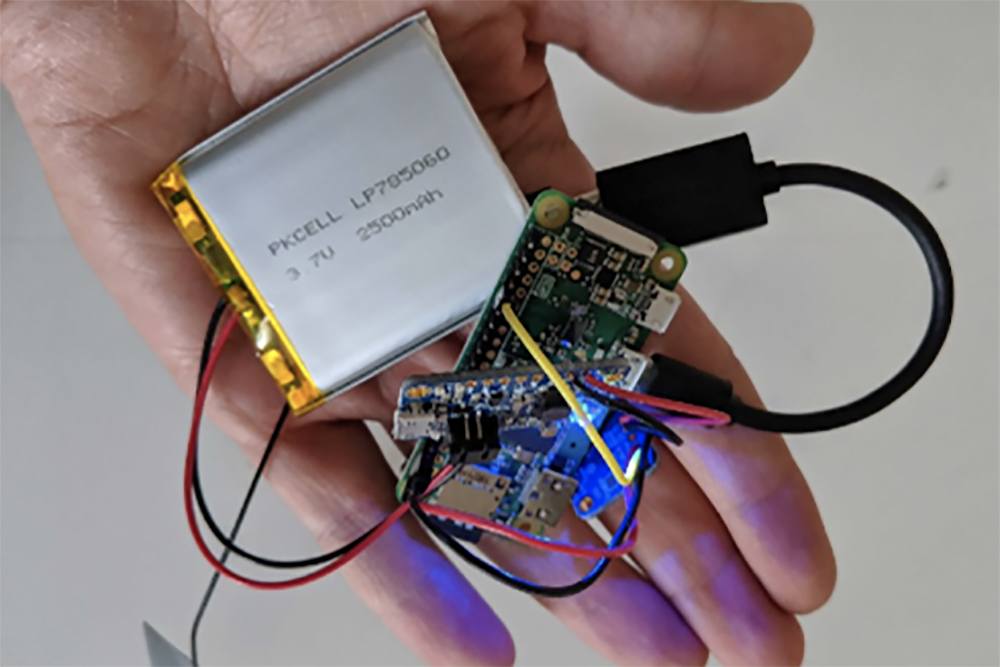
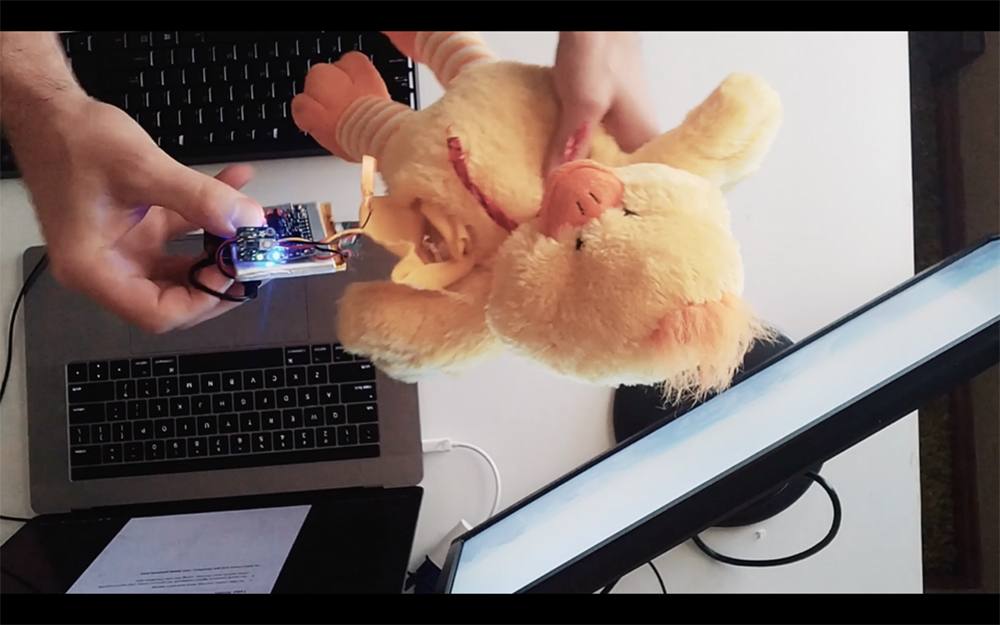
A victim organization receives a package in the mail, often containing items that look legitimate and relate to its everyday operations. However, a mini computer such as a Raspberry Pi is hidden somewhere in the package or its contents, along with a small battery and cellular antenna. Henderson says this equipment is available in DIY kit form and costs under $100.
Once activated, the device scans for WiFi networks and can be remotely-controlled to hack into them. It can also listen for network handshakes that are transmitted when users log in, and use that information to imitate the password and gain access to the network. This opens the door for the hacker to break into other computers or servers on that network.
The warship can also be used to create “evil twin” WiFi networks that mimic legitimate ones, tricking users into connecting to them and subsequently recording any secure information they transmit.
Admittedly, you’re unlikely to witness a warshipping attack unless you work for a high-profile corporation or government agency — these sophisticated attacks aren’t usually aimed at individuals. However, it’s interesting to study this trend, since it shows that physical security and digital security go hand-in-hand. If a criminal can’t breach digital defenses from the outside, he may use flaws in physical security (e.g. the company mailroom) to break them from the inside. A multi-faceted approach to preparedness is mandatory, whether you’re a Fortune 500 company or a small business employee.


