In This Article
Imagine the first volley of an all-out war between world superpowers. What images come to mind? If you grew up during the Cold War, you’ll probably think of ICBMs loaded with nuclear warheads detonating in major cities, wiping out millions of lives in the blink of an eye. Or perhaps you see guerrilla-style attacks with conventional explosives, dirty bombs, or even chemical or biological weapons as a greater possibility. While the prospect of any of these incidents is horrifying, there’s an increasing probability that a modern-day war between superpowers would begin with an entirely different kind of attack — a cyber-attack.
Before you roll your eyes and write off cyber-war as the sort of thing that only happens in science-fiction movies, consider some recent historical evidence — specifically, the devastating spread of ransomware known as Petya. This malware (i.e. malicious software), and its subsequent variant NotPetya, wiped out computers and computer-controlled systems around the world in 2016 and 2017. A statement from the Press Secretary of the United States called this “the most destructive and costly cyber-attack in history… causing billions of dollars in damage across Europe, Asia, and the Americas.”
By studying and analyzing the Petya and NotPetya malware, we can glean a better understanding of the very real possibility of a state-sponsored cyber-war between nations. Although these may have been the first cyber-attacks of this scale and severity, our ever-increasing dependence on technology ensures they won’t be the last.
The Origin of Petya
In Spring 2016, security researchers discovered a new piece of malware that began spreading to businesses through emails that posed as job applications. Each email reportedly contained a short message with a fake applicant’s photo and a link to a file that appeared to be a PDF document. If the email recipient downloaded and opened the file, the malware would be installed and the computer would crash immediately with a blue screen.
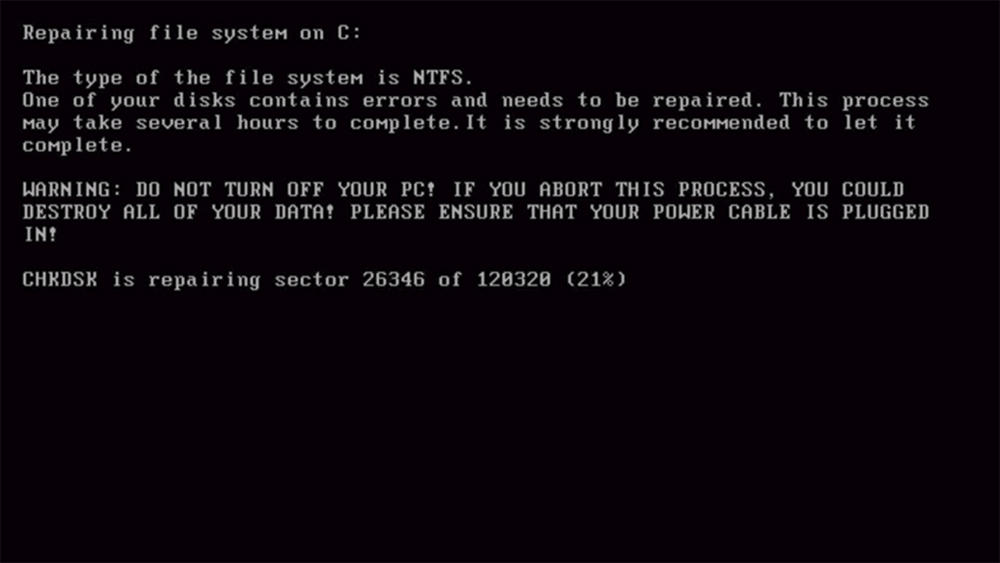
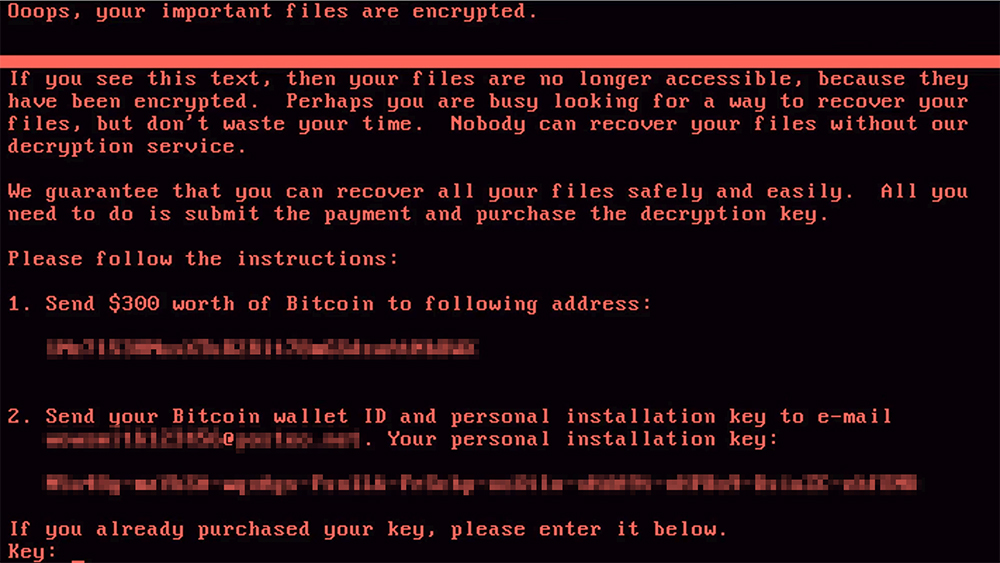
Once the the computer was rebooted, a message would appear stating that the computer’s file system was being repaired. This closely resembles an actual Check Disk message generated by Windows in the event of a system error, so many users assumed it was not out of the ordinary. However, the process actually encrypts all documents and files on the infected computer.
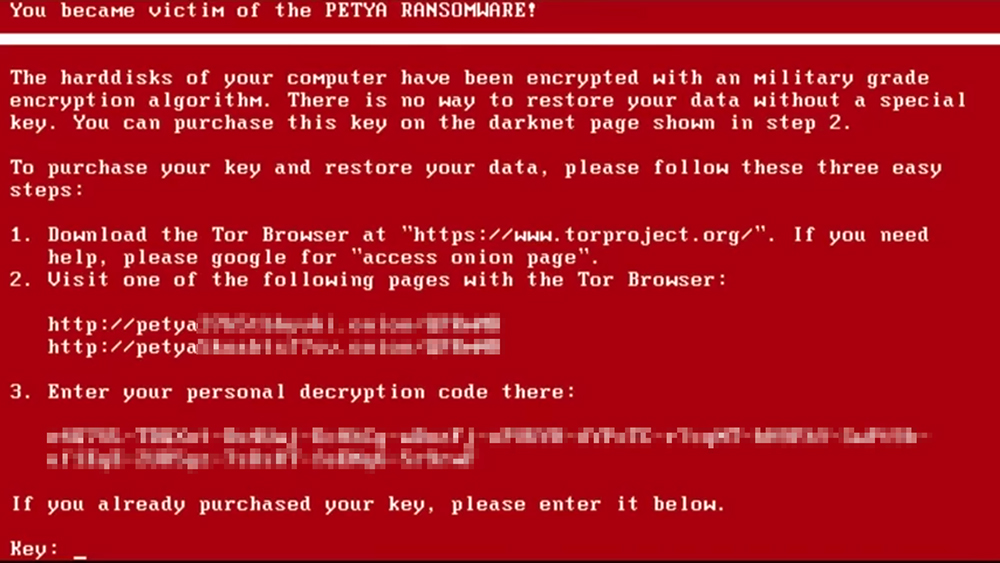
Once the process completed, a message would appear stating that the computer had been infected by Petya (a reference to one of the Soviet weapon satellites in the James Bond movie GoldenEye) and that all data would be permanently lost unless a Bitcoin payment was sent to those responsible for the attack — hence the name ransomware.
The attackers promised to provide a decryption key that would unlock the computer after the payment equivalent to roughly $900 was received, but the encryption was generally irreversible through other means. In other words, any computer affected by Petya was instantly unusable and all data on it was locked. For most users, the only option was to wipe the hard drive, permanently erasing all the files on the computer.
The following video shows how a 2016 version of Petya functions:
As ransomware, these early versions of Petya were tools for monetary gain, holding computers hostage in the hope that panicked users would give in to attackers’ demands. But Petya hadn’t made major headlines yet. This was only the beginning.
NotPetya – The Malware Evolves
On June 27th, 2017, a new cyber-attack began. It was based heavily on the earlier versions of Petya, and used a similar mechanism of encrypting files after a computer was rebooted. However, according to a statement by Microsoft, this variant was “more sophisticated”. Security researchers would eventually name it NotPetya.
The first cases of NotPetya infection have been traced back to MEDoc, a Ukrainian tax and accounting software company. Later investigation would show that hackers stole an employee’s login credentials and added code to MEDoc, causing its update process to distribute NotPetya and start the infection.
Unfortunately, computers with MEDoc software were not the only victims — this was only the first wave of the cyber-attack.
An especially insidious new characteristic of NotPetya was its ability to spread through networks via a security vulnerability in Windows. After a computer was infected, the program would automatically search for all other accessible computers on the local network and install itself on them. This meant that the malware could spread from one computer to infect every PC in an entire company.
Unlike the original Petya, researchers have concluded that NotPetya’s goal was not monetary. In fact, Symantec concluded that the randomly-generated installation key has no relationship to the disk encryption and “the disk can never be decrypted”. Rather than considering NotPetya ransomware, Symantec calls it a “wiper” — malware designed to irreversibly destroy files and disable computers. This was no longer simple extortion, it was a weapon.
Evidence of Targeting
MEDoc, the initial vector for the attack, is a Ukrainian company whose software is widely-used in that country. According to Reuters, “M.E.Doc is used by 80 percent of Ukrainian companies and installed on about 1 million computers in the country.” This made it an ideal means of distributing the malware within the country.
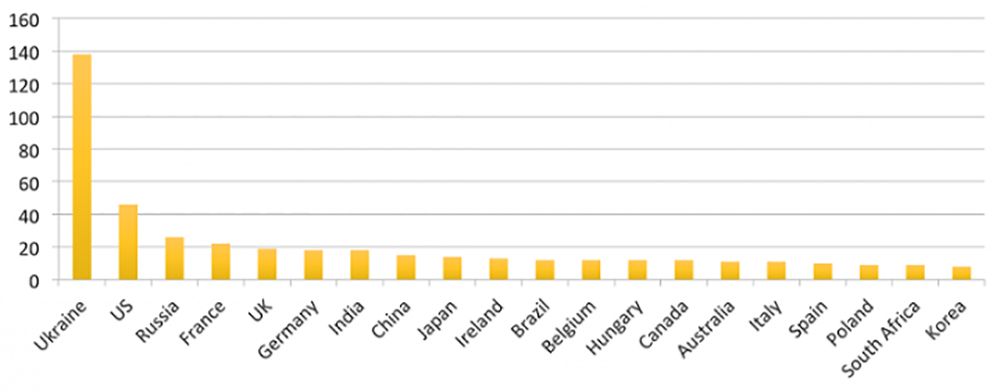
The following graphic from Symantec shows a comparison of the number of organizations affected by NotPetya in 20 countries:
In addition to the initiation of the NotPetya attack in Ukraine and the disproportionate number of Ukrainian computers affected by the malware, even the date of the attack bears some significance. June 28th is Ukraine’s Constitution Day, a day which celebrates the country’s independence. This would be comparable to a major attack on the United States occurring on the afternoon of July 3rd.
Given this information, security researchers soon concluded that Ukraine was the primary target of the NotPetya attack, and that its spread to other countries could be considered either diversion or simple collateral damage. Craig Williams, senior technical leader for Cisco’s Talos intelligence unit told Reuters, “This wasn’t made for any other purpose but to destabilize businesses in the Ukraine.”
Possible State Sponsorship

Considering the long-running conflict between Russia and Ukraine, analysts began to speculate that the attack may have originated in Russia, and shortly after the attack, Ukrainian officials made statements accusing this connection. Anton Gerashenko, a member of Ukrainian Parliament, called it “just one part of the hybrid war of the Russian empire against Ukraine.”
Official statements from the White House and the UK Foreign Office also blamed Russia for the attack — the former said it was “part of the Kremlin’s ongoing effort to destabilize Ukraine” and “a reckless and indiscriminate cyber-attack that will be met with international consequences.” A Kremlin spokesman responded by denying responsibility for these attacks and calling these accusations “Russophobic”.
Ironically, the EternalBlue security vulnerability that made NotPetya’s spread through networks possible was initially developed by the U.S. National Security Administration (NSA). Brad Smith, President of Microsoft, clearly stated that the vulnerability was “stolen from the NSA” before being leaked to the public and eventually being utilized by the criminals behind this and other ransomware attacks. He also wrote that there is “a completely unintended but disconcerting link between the two most serious forms of cybersecurity threats in the world today – nation-state action and organized criminal action.”
Conclusions

Regardless of the origin of NotPetya, it is clear that this malware was intended to cause catastrophic damage on a national (and potentially international) scale. It succeeded in this aim.
Within the Ukraine, computers at numerous government agencies, hospitals, banks, transit systems, utility providers, and even the radiation monitoring system at Chernobyl suddenly went offline. Outside the Ukraine, numerous multinational organizations were also affected. DLA Piper — one of the world’s largest law firms with 3,600 lawyers across 40 countries — instantly went into lockdown mode and lost millions of dollars as a result of NotPetya. Other multi-national organizations affected by NotPetya include Danish shipping company Maersk, German shipping company DHL, U.S. pharmaceutical company Merck, French construction company Saint-Gobain, and India’s largest shipping port JNPT.

While the widespread use of computers and technology has certainly made our lives easier, it has also left us vulnerable to cyber-attacks that can cause sudden disruptions in the availability of resources we rely on. Cyber-attacks such as Petya can interfere with our personal PCs, but more sophisticated variants such as NotPetya have proven themselves capable of shutting down financial institutions, electrical infrastructure, shipping and manufacturing of consumer goods, medical treatment, and other essential services. Without these, our polite society would quickly descend into chaos.
A cyber-war started by a rogue terrorist group or criminal organization is a substantial threat, but one sponsored by national funding could be truly devastating, even if you’re not over-reliant on personal electronics. Fortunately, if you’re prepared for a large-scale emergency situation, the cause — whether it’s a natural disaster, conventional attack, cyber-attack, or Terminator-esque sentient cyborg uprising — will be irrelevant.