Personal interaction is a fine balance of trust and suspicion. On one hand, we shouldn’t be too trusting of strangers, as this may allow malicious individuals to take advantage of our blind trust. On the other hand, we can’t exactly go through life cynically doubting and scrutinizing everyone we know at all times — that would be sheer paranoia. In order to find a middle ground between trust and suspicion, it’s important to recognize warning signs. A heightened sense of awareness can help you know when to be suspicious, and when to let your guard down a little.

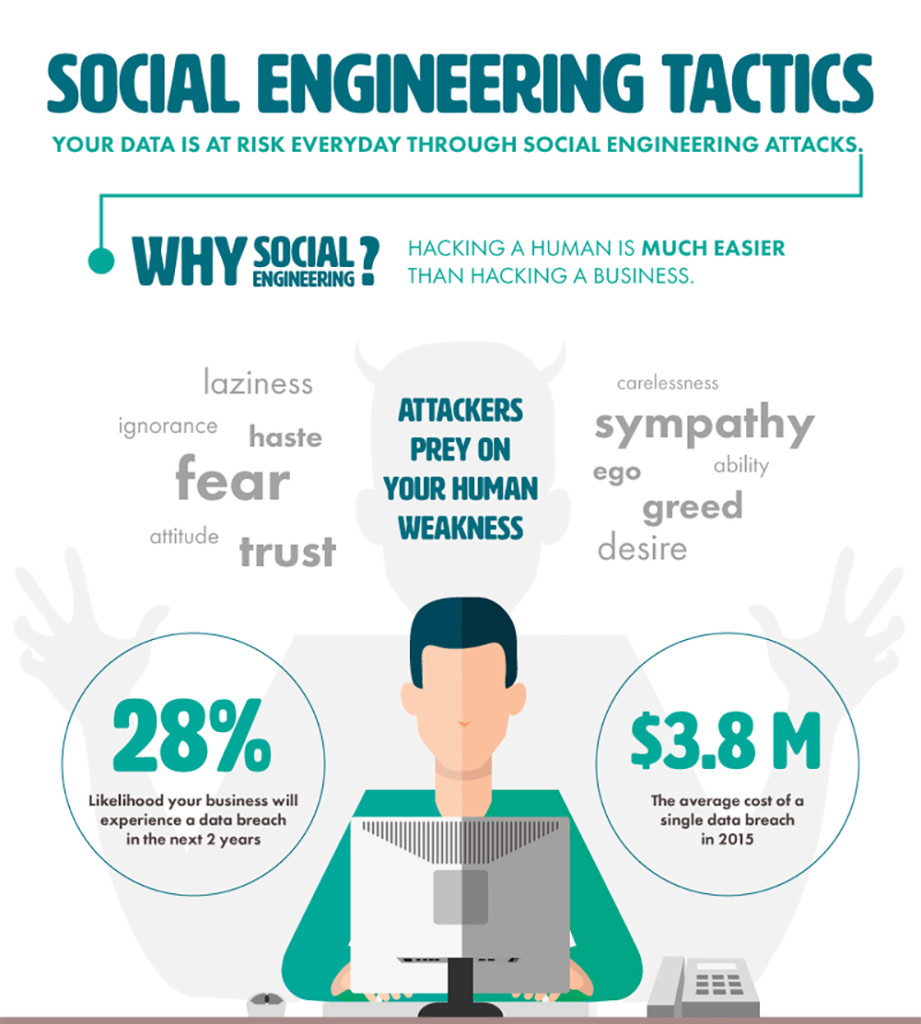
A technique known as social engineering is used by criminals to exploit the grey areas in this balance of trust and suspicion. Social engineering is defined as “the art of manipulating people so they give up confidential information.” In essence, social engineers prey on those who tend to sway too far towards trust and gullibility, and use smooth talking charisma to steal credit card information, account passwords, PIN numbers, and other sensitive data. A social engineer may pose as a customer service associate, technician, security guard, family member, or other trusted figure.
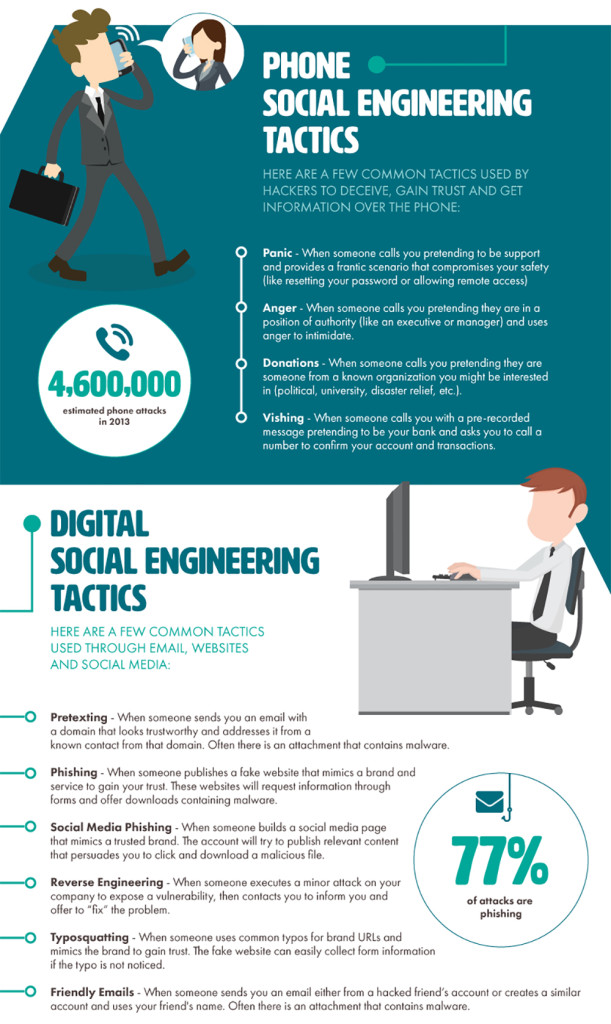
The term social engineering is most often used in reference to internet-based attacks — phishing, a technique we’ve discussed in the past, falls under the umbrella of social engineering. Online social engineering has played a major role in some high-profile scandals recently, such as the DNC email leaks.
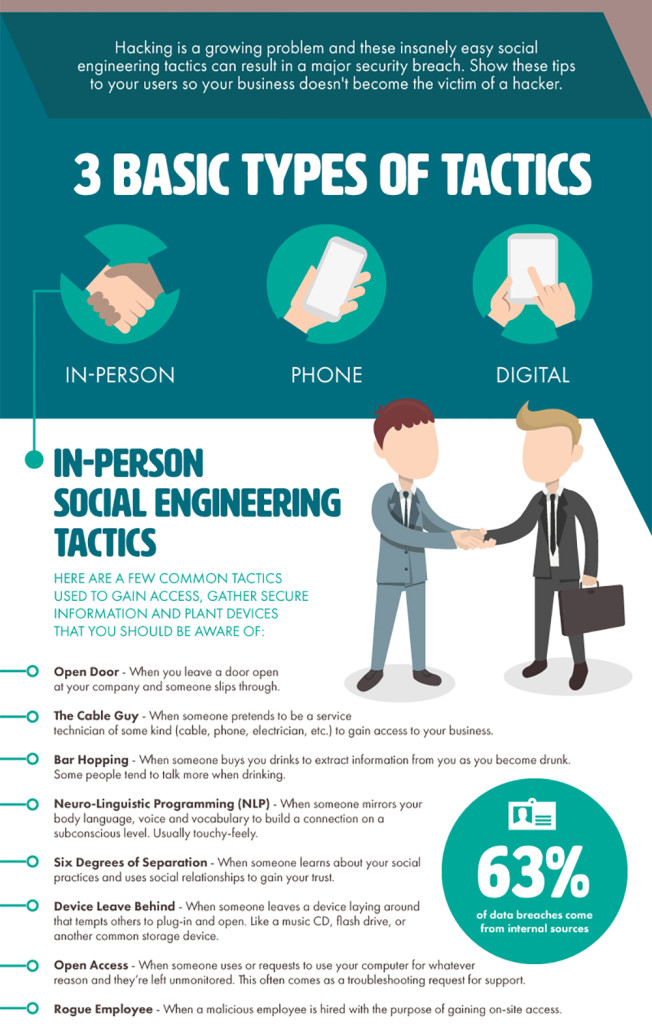
However, social engineering doesn’t occur solely on the web. It can happen over the phone, or even through in-person interactions. The following infographic from SmartFile shows the three basic types of social engineering tactics, and can help us identify the warning signs of an attack. Click here for a full-size version.