If you’ve ever used a computer, you’re probably aware of the term USB. The acronym stands for Universal Serial Bus, and for good reason—it’s found just about everywhere. This standard connector is present on virtually every desktop and laptop computer produced in the last two decades, as well as many other electronics, including TVs, car stereos, printers, and retail point-of-sale systems. Smaller versions of the port are found on portable electronic devices, such as smartphones, tablets, and digital cameras.

Looking at this situation from a security standpoint, it’s easy to see the vulnerability here. When almost every device uses the same universal connector, it’s easy for malicious individuals to exploit that crack in the armor to damage or destroy USB-compatible devices. A tool known as the USB killer has gained recognition for achieving this goal in seconds, and it looks just like any other ordinary USB thumb drive.

Disclaimer: This article is presented for educational and informative purposes only. USB kill sticks have many potentially harmful and illegal uses, which we obviously do not condone. Use this knowledge to protect yourself and your electronic devices from potential vulnerabilities.
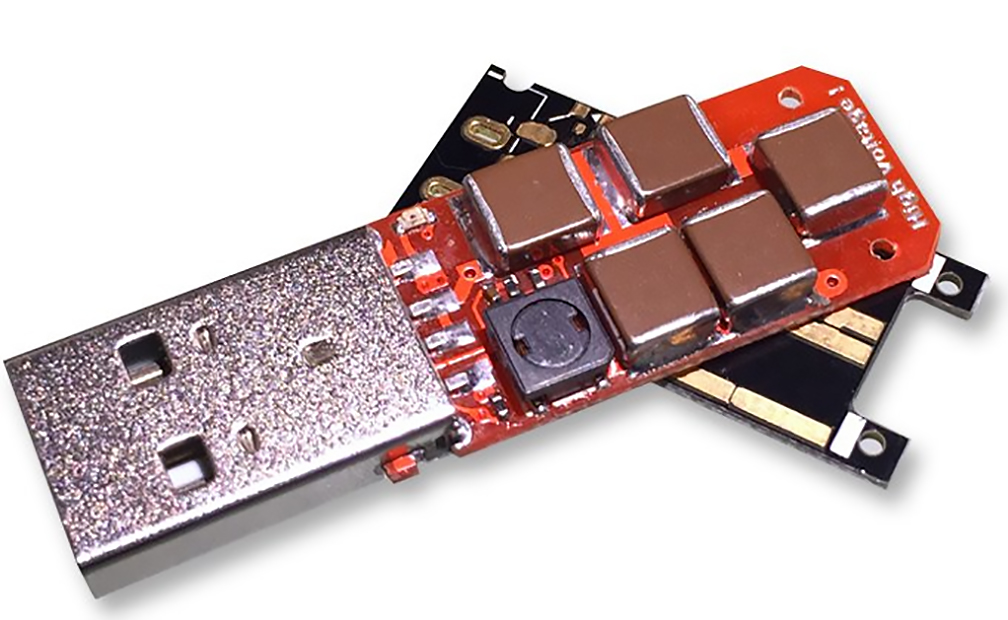
This product was developed in 2015 by a Hong-Kong-based security research team, and is sold through USBkill.com for a mere $50. It looks like an ordinary USB flash drive or thumb drive, encased in a white plastic shell with only a vaguely-skull-shaped logo revealing its true purpose. Inside the plastic case, there’s a small circuit board that contains a network of capacitors, which are charged and discharged many times per second via the host device’s USB power. This delivers a series of instant 200-volt death blows to any connected device.
Here’s a video of the USB Killer in action. First, the presenter connects the device through a USB Killer Tester, to prove it works without damaging the computer. Then, once the tester is removed, the kill stick immediately shorts out the laptop’s motherboard, permanently disabling it:
The implications of such a device are clear: any exposed USB port is a potential attack vector. With an inexpensive and pocket-sized device, a malicious individual can destroy thousands of dollars of computer hardware in the blink of an eye.
The developers of this device recognize the problem, and passed out samples to computer hardware companies, so they could add protection against such an attack. However, according to the USB Killer team’s blog, these warnings have mostly been ignored:
“To this day, according to our testing, the only company that releases hardware protected against a USB power-surge attack is Apple, on their Laptop and Desktop ranges. This means – despite adequate warning, and time to respond – the majority of consumer-level hardware manufacturers choose not to protect their customer’s devices. We are disheartend [sic] by this lack of respect for customers.
As is standard in the InfoSec industry, we are releasing the USB Kill publically [sic], after one year of disclosure. We hope the attention will force manufacturers to respect a customer’s investment in their product, and work to resolve the issue.”
For ordinary individuals, the USB Killer team makes the following recommendations:
“Individuals have steps immediately available:
- Don’t trust unknown hardware
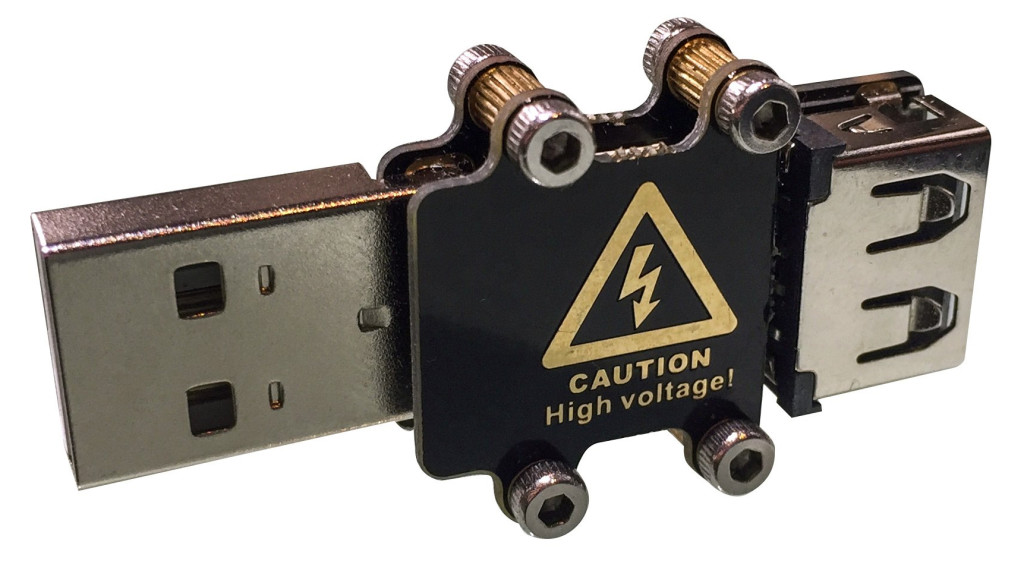
- Use a USB condom
- Physically cap USB ports, similar to covering webcams
As others have mentioned: the vulnerability, like the tool, is a blunt instrument. Like any blunt instrument, it can be used constructively or destructively. Our stand-point: we strictly forbid abusive use of the tool.”
For more information on the USB Killer and how it works, visit USBkill.com.