Imitation is a powerful skill, and one that malicious individuals will use to their advantage. In the security world, the strategic use of manipulation techniques for criminal purposes is known as social engineering — you can read more about social engineering and its sub-categories in our previous article, Social Engineering: 5 Manipulation Techniques. Phishing is one common technique in which criminals attempt to steal sensitive information from unsuspecting victims by imitating a trusted person or organization.
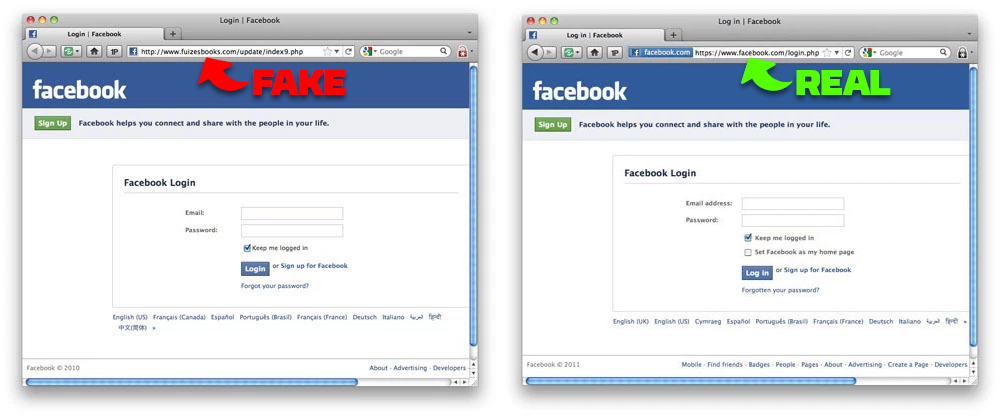
In phishing scams, attackers will often set up elaborate email campaigns, web sites, or phone systems that closely resemble those used by legitimate entities. These can include popular tech companies like Facebook or Google, banks, or government organizations like the IRS. The victim often thinks they’re communicating with the real deal, but every username, password, or credit card number submitted through these digital facades is immediately taken and exploited. This can result in severe financial losses or stolen identities.
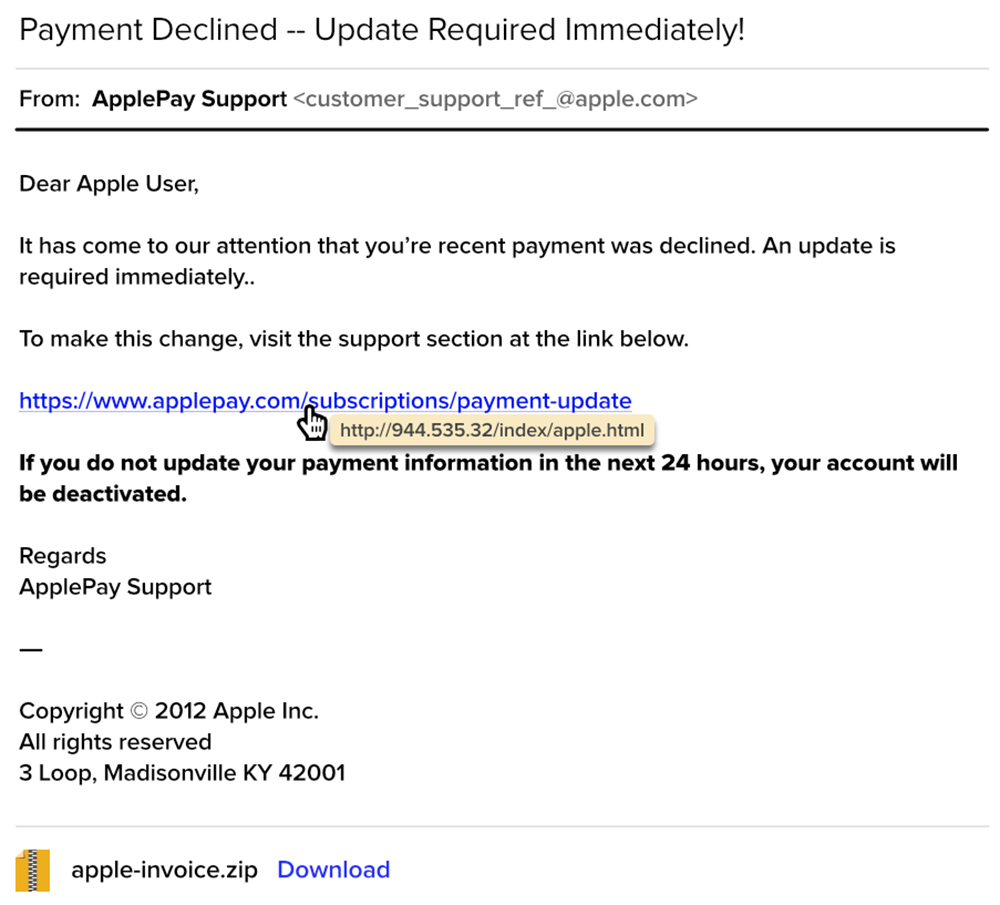
Fortunately, with a healthy dose of skepticism and an eye for detail, it’s often possible to detect these attacks before you fall victim to them. If you want to test your skills, check out the email image below and count how many phishing red flags you can spot:
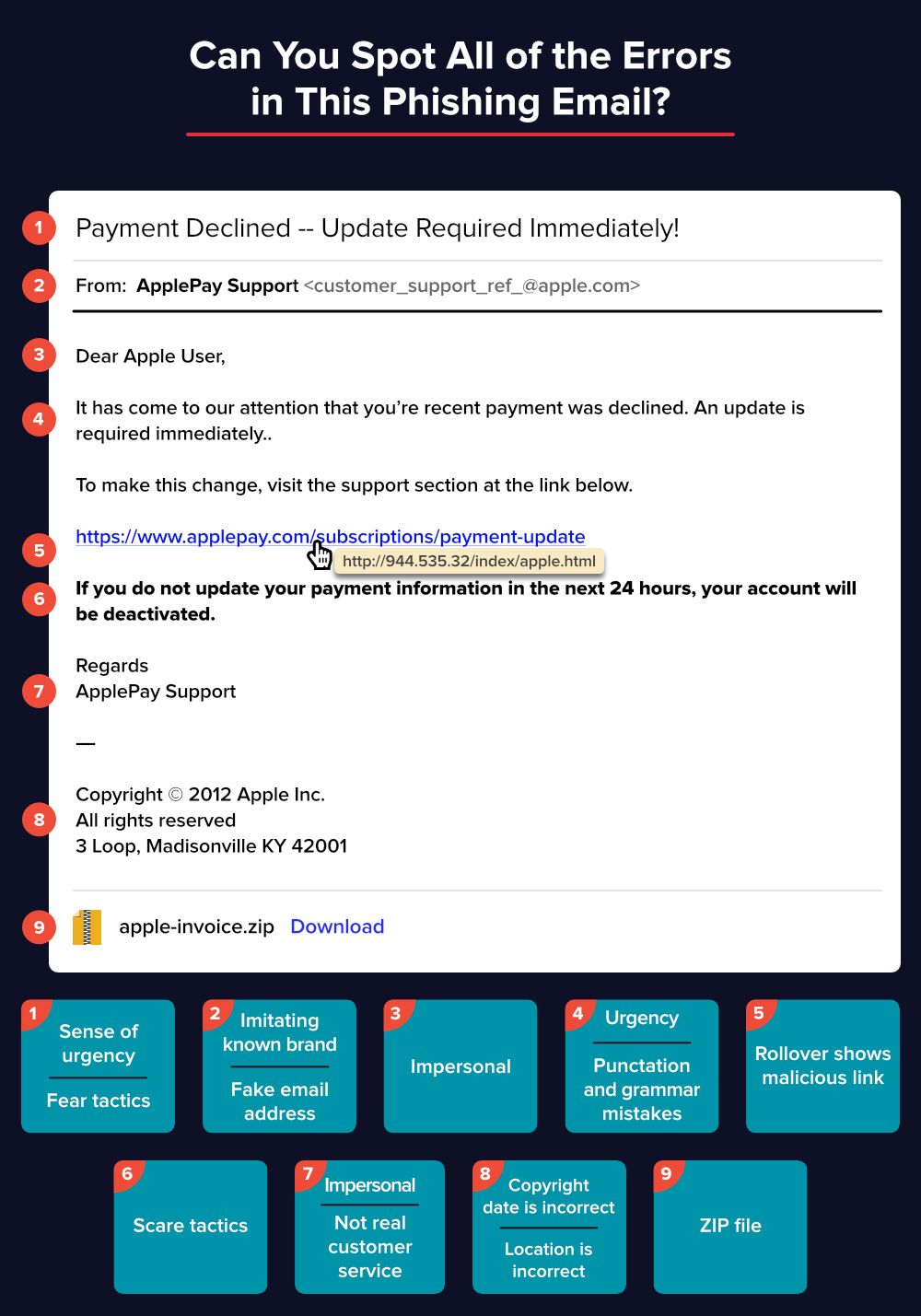
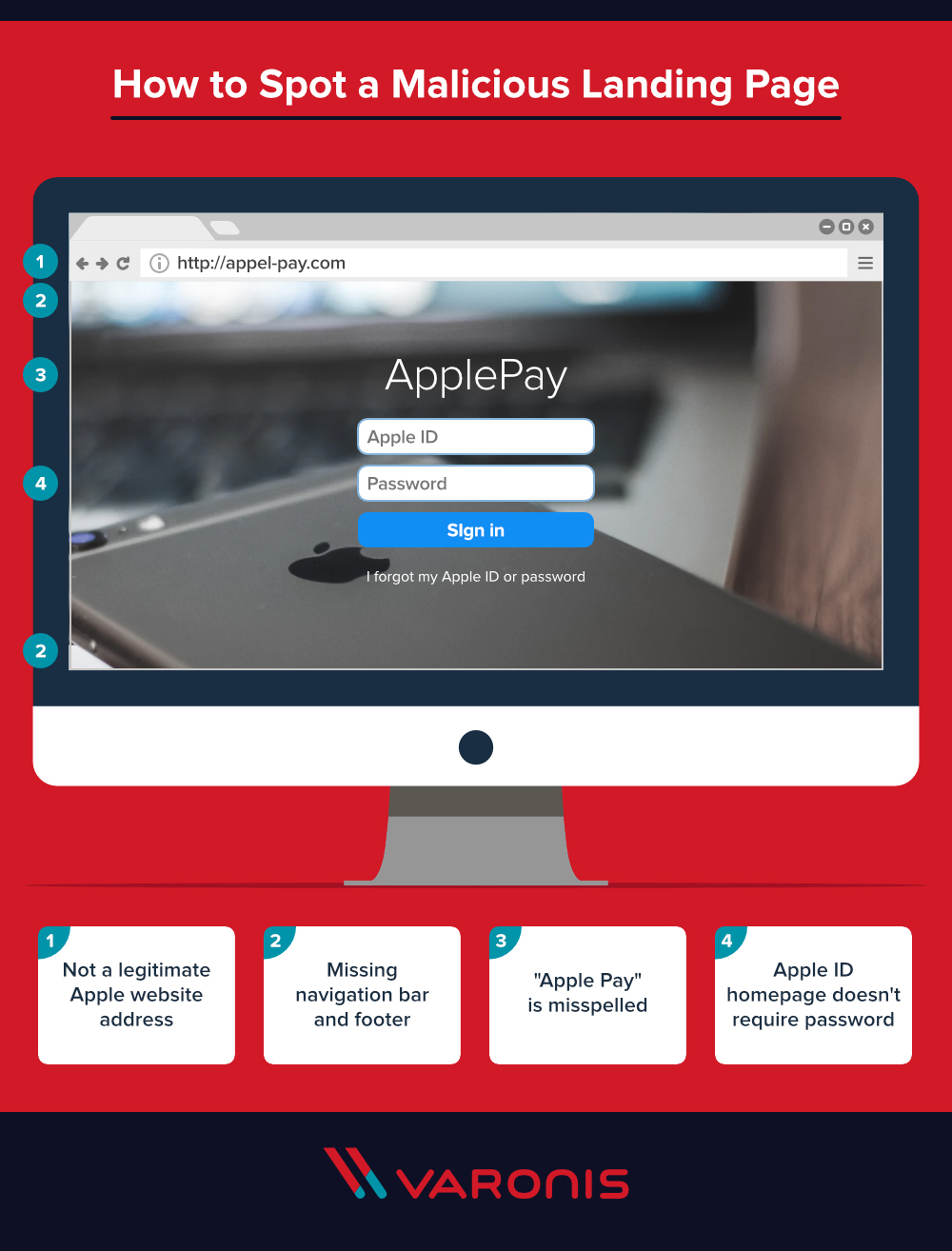
There are at least 9 potential warning signs in this screenshot that should make you skeptical. For an explanation, check out the following infographic from Varonis. It lists the signs in the phishing email, and also shows some of the things to look for on a malicious landing page (i.e. the fake web page you’d end up on if you clicked the link in the email above). Click here to download a full-size version of this infographic.
For a much more detailed explanation of these phishing tactics, and other information about digital security, check out this blog post from Varonis.