In This Article
Most of us have put a substantial amount of thought and effort into protecting our homes against intruders. You might have an alarm system, a doorbell camera, high fences, a dog that barks loudly, upgraded door locks and striker plates, a bedside gun, or all of the above. You’d certainly be angry if an uninvited stranger opened your door and started going through all your drawers, taking pictures of your valuables, looking over your shoulder as you type, and listening to your private conversations.
A physical intrusion of that magnitude seems absurd, but in the digital space, it’s more common than you might think. It’s possible for someone to break into most WiFi networks with nothing but a laptop, a modicum of research skills, and (depending on your security measures) some patience. Hackers can find targets from a neighboring house or apartment, on foot, or inside a vehicle (known as wardriving). You may not even know an intrusion is happening — unlike a burglar kicking in your door, an uninvited guest on your wireless network can easily go unnoticed.
The Dangers of Poor Network Security
In the best case, an intruder may just be freeloading off the internet service you’re paying for, using your bandwidth and slowing down your devices. In worse cases, they could be skimming your passwords and personal information, or committing crimes from within your network. Just imagine law enforcement officers pounding on your door to ask why child porn was being distributed from your network. That could conceivably be the result of a criminal exploiting a major lapse in your digital home security.
The dangers of poor network security aren’t just local, either. Last year, security researchers learned that an “advanced, likely state-sponsored” malware known as VPNFilter had affected at least 500,000 routers and other network devices in 54 countries. Most of these devices were victimized because of “known public exploits or default credentials that make compromise relatively straightforward.” Like the devastating cyberattack known as Petya, analysts have speculated this malware originated in Russia and may have been at least partially targeted at the Ukraine.
According to the cybersecurity experts at CISCO Talos, “[VPNFilter] has a destructive capability that can render an infected device unusable, which can be triggered on individual victim machines or en masse, and has the potential of cutting off internet access for hundreds of thousands of victims worldwide.” It also gave attackers the ability to harvest website credentials and monitor network traffic.
Fortunately, protecting against most of these attacks is often as simple as ensuring your router is frequently updated and equipped with a few key security features. Read on to find out how.
Routers & Modems

Before we go any further, it’s worth clarifying the difference between a router and modem. If you already know this difference, go ahead and skip the remainder of this section.
A modem enables you to connect to the internet through your internet service provider (ISP). The modem receives signal from outside your home over a coaxial cable (for cable modems) or telephone wire (for DSL modems). Standalone modems typically have only one output port for another device — this usually connects directly to your router.
A router distributes (or routes) that connection to various other wired and wireless devices in your home. To borrow a simplified metaphor from Gizmodo, the router is like a front-desk receptionist at a large office building. It’s easy to walk through the front door (modem) but the receptionist (router) is the single point of contact who will determine who you are and where you’re going in the building. If your credentials are incorrect or you’re asking to meet with the wrong person, security (the router’s firewall) won’t let you go any further. The router is therefore your main point of defense — if someone gets past it, they can cause all sorts of havoc.

It’s possible to get a router/modem combination unit with all-in-one functionality — many people get these as rentals or loaners from their ISP. However, if you’re looking to maximize your security, we’d advise you to buy your own separate, high-quality modem and router. This can help you maximize the speed you’re paying for, and also improve reliability. If one of the devices starts having issues, it’ll be easier to troubleshoot and replace the culprit. Make sure the modem you buy is on your ISP’s approved list for your internet package (check the company’s web site or search “[provider name] modem list”).
Accessing Router Settings
For the rest of this article, we’ll focus on your router, since it’s your primary line of defense. We’ll also assume it’s one you’ve purchased and have complete administrative control over.
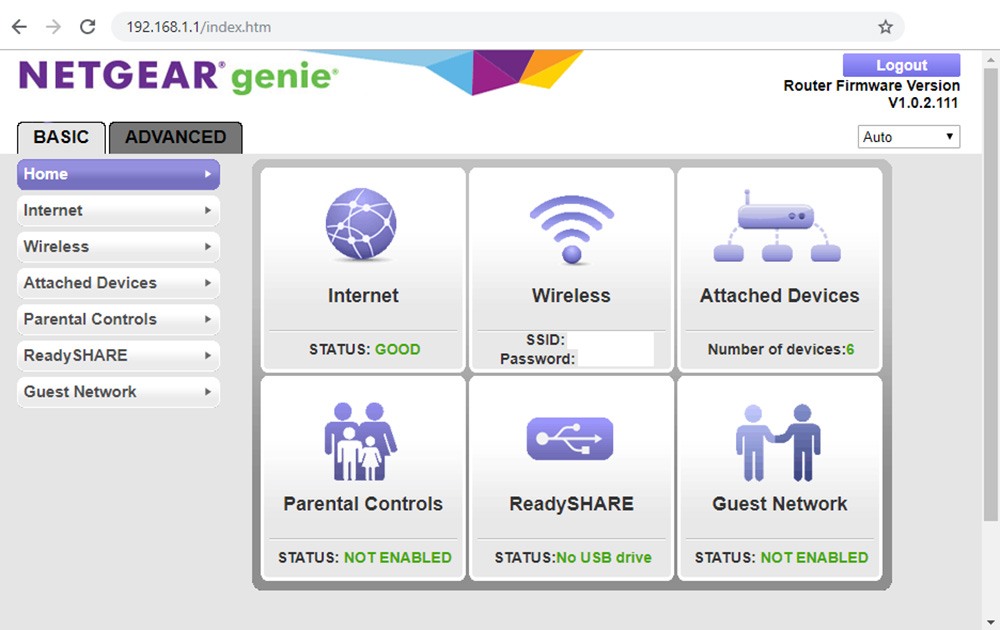
To figure out how to log in to your router’s control panel, check the instruction manual. Most of the time it’s as simple as connecting a device, opening the internet browser, typing in 192.168.0.1 or 192.168.1.1 into the address bar, and entering the username and password from the instruction manual. If you can’t log in for any reason, you may need to press the factory reset button on your router — this will reset the admin username and password to the factory default, and clear any other custom settings.
1. Make Sure Firmware & Hardware is Up-to-Date
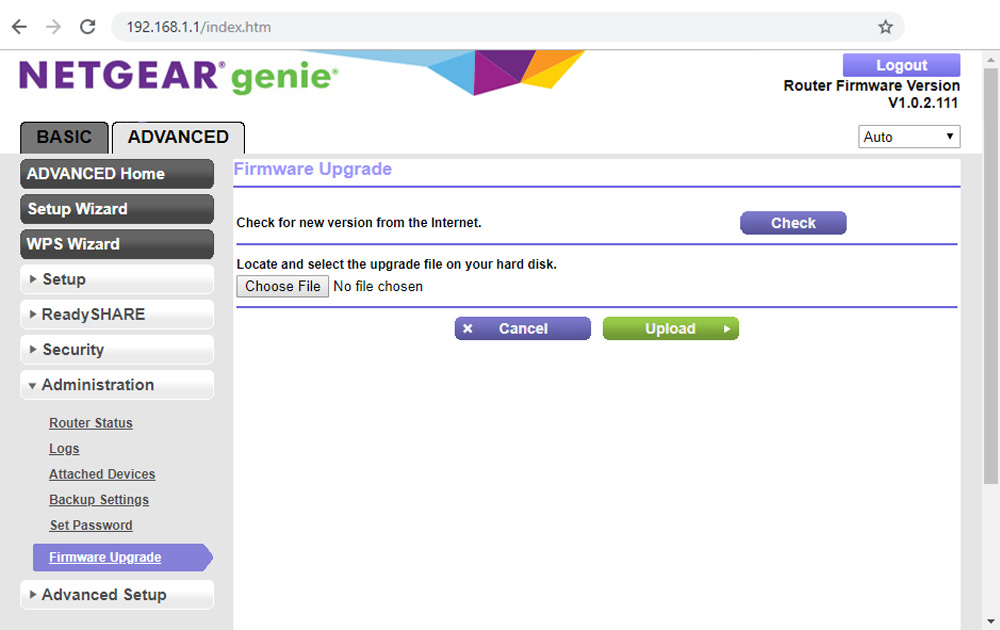
Once you’ve connected to your router, the first thing to look at is the version of its firmware (the software that controls it). There’s usually a button to check for updates — click it, and take a few minutes to install the latest firmware version that’s available. These updates often fix security vulnerabilities that were discovered after the router was released, such as the KRACK exploit that allowed hackers to breach networks in 2017.
If no updates are available, or if you’ve owned your router for more than 3-4 years, it may be time to upgrade to a newer model. Router technology moves quickly, so upgrading to a new (but not bleeding-edge new) model every few years will give you the latest security features. In many cases, it’ll also improve connection reliability and speed by meeting the latest industry standards.
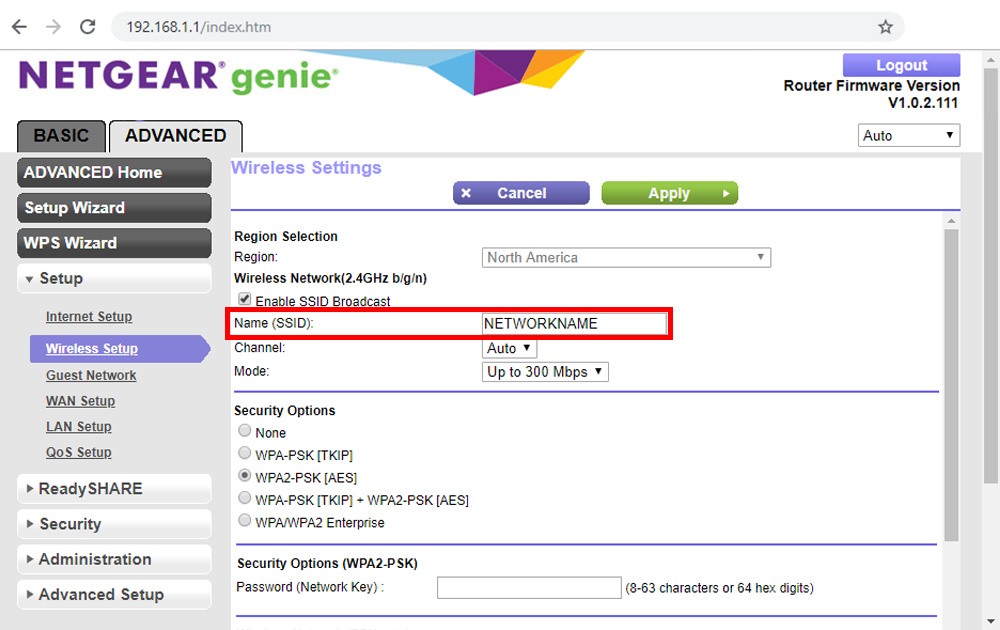
2. Change Your Wifi Network Name (SSID)
Here’s an exercise to try at home: get your cell phone or laptop and check the available WiFi networks in your vicinity. Most of them will be password-protected, but the network names (also known as SSIDs) will still tell you quite a bit of information. “Smith network” tells you the owner’s last name so you can look up their address and learn more about their family or business. “Netgear” tells you the type of router so you can research security exploits for it, and also indicates that the device is probably still using the manufacturer’s default settings (and admin username/password).
To avoid giving away information about your network, simply change the network name to something that has nothing to do with your family or device. If you’re especially crafty, you could do some misdirection and call it “Linksys” when your router is actually a Netgear. That way, if someone tries to research device-related exploits, they’ll be sent on a wild goose chase. (Don’t bother with comedy names like “virus distribution network” or “FBI surveillance van” — you’re not scaring anyone off with those.)
Hiding your SSID is an option that makes your network invisible to the public, but it’s more of an inconvenience to your guests than an effective security measure. It’s very easy to discover hidden networks with a single command in Windows, and anyone who might try to hack your network is likely to know this. Still, you might get lucky and avoid the attention of less-experienced hackers.
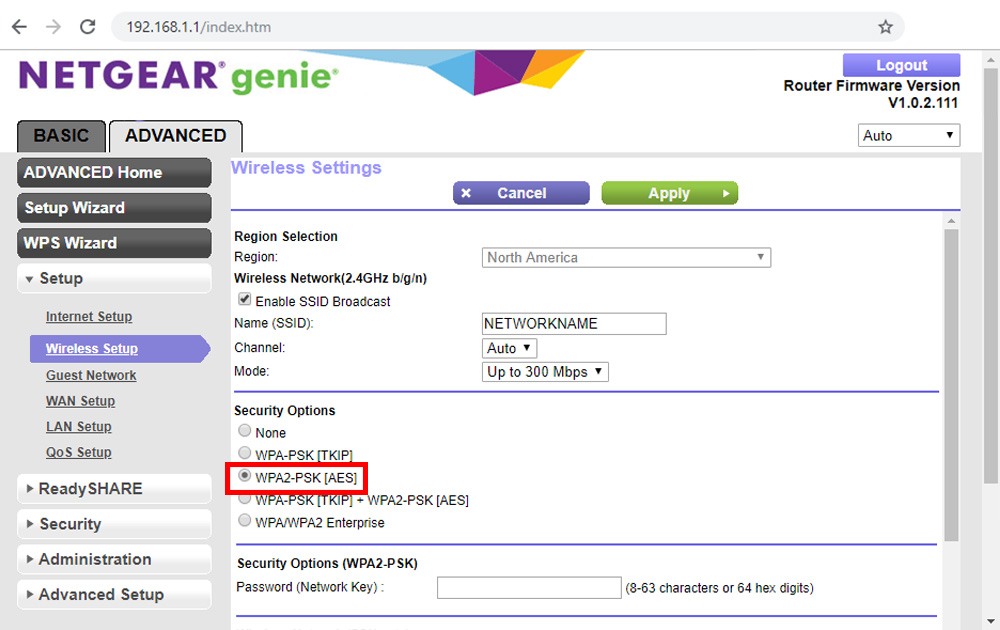
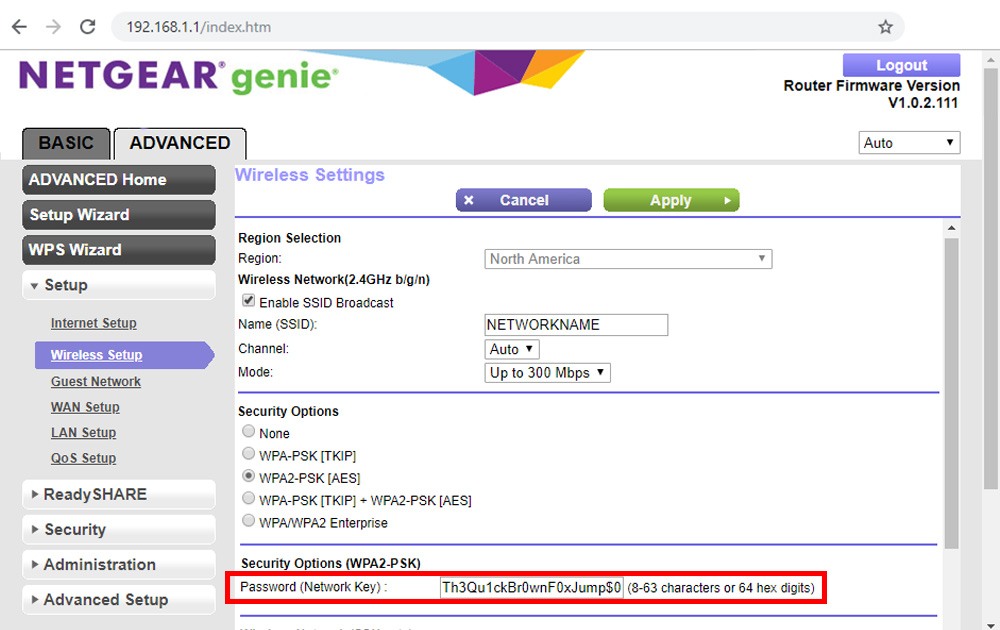
3. Use a Strong Encryption Protocol
If you’ve ever configured a new WiFi network, you’ve probably seen a few options next to the password field. These might include None, WEP, WPA, WPA-TKIP, WPA-AES, and WPA2-AES. The “none” option means an open network with no password — we shouldn’t have to explain why that’s a terrible idea. The other options are security protocols. You can think of these like locks on the virtual door to your network.
WEP is the oldest and trivially easy to crack, taking only minutes to breach with commonly-available programs. WPA (as well as the newer WPA-TKIP and WPA-AES variants) are better choices, but they’re still not ideal. WPA2-AES is the industry standard and the most secure option of these choices. By ensuring your router is set to WPA2-AES and following the password recommendations below, you’ll be placing a huge roadblock in the way of anyone looking to break into your network.
(A newer protocol, WPA3, is on the horizon, but will likely need some more work before it’s considered a true security improvement on WPA2-AES.)
4. Set Secure Passwords
Immediately after setting the SSID and encryption protocol, you’ll need to set secure passwords for your WiFi network and router. Do not use the default credentials. Unless this is your first day on the internet, you should know that common words like “password” and numbers like “12345” are weak. Many people go to the opposite end of the spectrum and think that passwords need to be complex gibberish like “Q7#eN8*52hW2k$35” — fortunately, that’s not necessarily the case.
A happy medium is to start with a long, complex, and memorable phrase. Ideally it should be obscure or totally unique. Avoid famous lines like “franklymydearidontgiveadamn” or “ilovethesmellofnapalminthemorning.” Once you have a phrase, incorporate capital letters, symbols, and numbers throughout the phrase to make it more difficult to guess. In the article Tips for Better Passwords, Consumer Reports gave the example, “Th3Qu1ckBr0wnF0xJump$0verTh3LazyD0g.” This method produces a passphrase that’s secure, but not impossible to memorize like the gibberish example above.
Diceware is another method that involves rolling dice to generate a randomized string of numbers that are cross-referenced with a word list to create a phrase.
You should create secure passwords for your WiFi network(s) as well as your router’s administrator control panel. Use different passwords for each. This way, someone can’t gain access to your WiFi network through legitimate means (i.e. visiting your house) and sneakily disable the router’s security features while they’re logged-on.
5. Monitor Connected Devices
Even if you’ve done all these things, it’s unlikely that someone will defeat your security measures, but it’s not impossible. You should therefore know how to check the devices that are currently connected to your WiFi network — if you don’t recognize one or more of them, you should dig deeper to see if your network has been compromised.
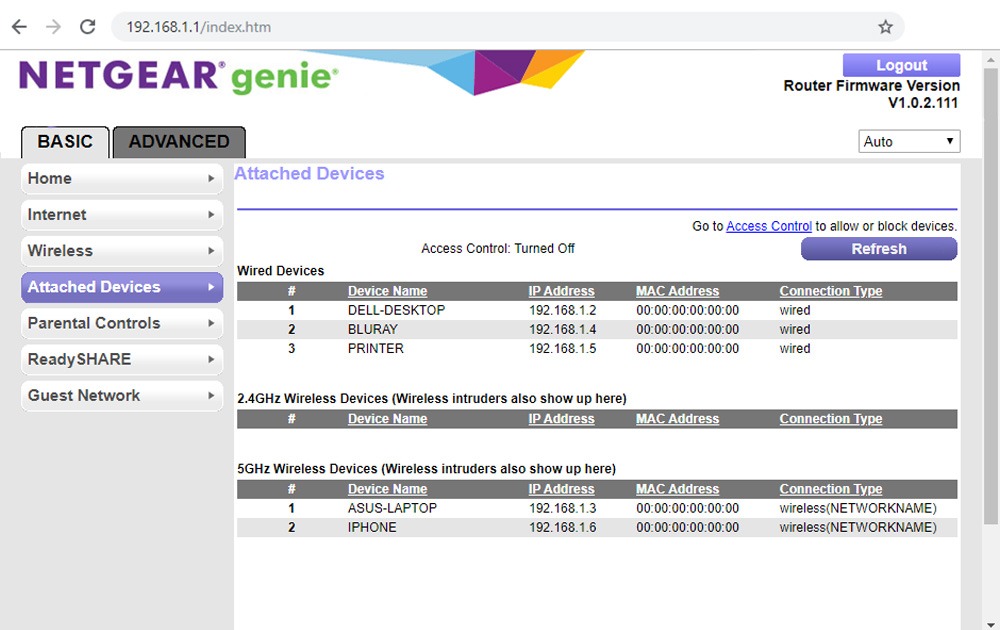
Most routers have a “connected devices” menu that will list the names and MAC addresses of devices that are connected to the router.
The name is set by the user or manufacturer, and can be almost anything — for example “DELL-DESKTOP” or “IPHONE.” Don’t trust that this is an accurate representation of a device, since many device names can be changed at will.
A MAC address is a string of 12 numbers and letters that serves as a unique* identifier assigned to a specific internet-connected device — for example, 08:6D:41:00:00:01. The first 6 characters provide information about the company that manufactured the device (or its internet adapter), and this information can be checked using sites such as WireShark.org. In the case of the example, 08:6D:41 comes back as “Apple, Inc.”
*MAC addresses are not always unique — hackers can scan for trusted devices on a network and imitate or “spoof” the MAC address of one of those devices.
Occam’s Razor applies here — if you don’t recognize a device, don’t freak out and assume you’ve been hacked. That device could be anything from a tablet or e-reader to an Internet of Things device like a smart washing machine (those unnecessarily-smart devices pose threats of their own, but that’s a topic for another day). Use the name and MAC address to narrow down what it is.
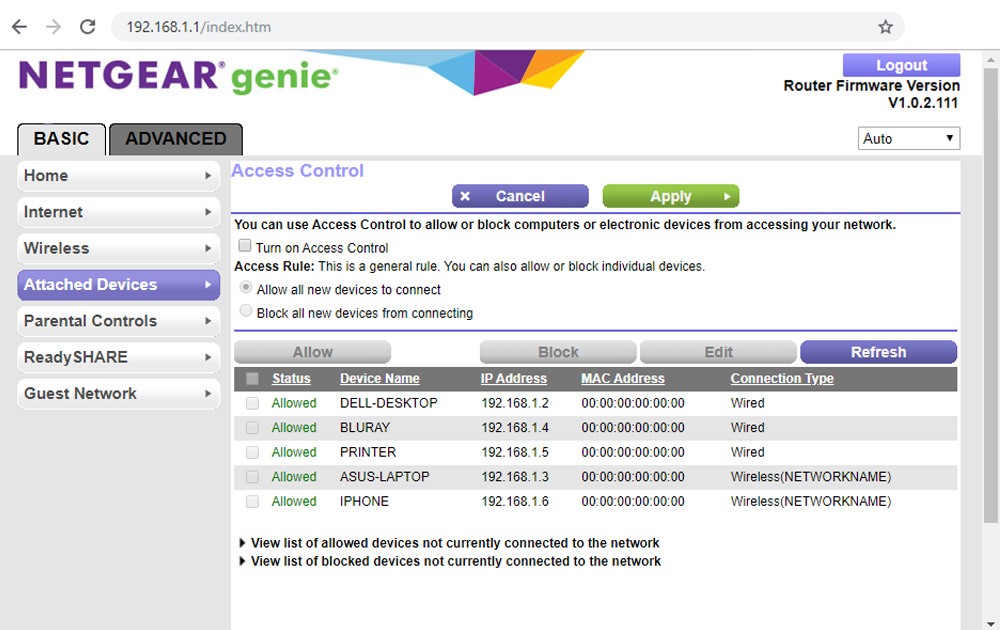
If it still seems unusual, you can use your router’s MAC address filtering to block certain devices, or block all devices that aren’t on a preset whitelist. But as with hiding your SSID, this can become a hassle that’s more trouble than it’s worth, especially if friends regularly visit and try to use your network. Help Desk Geek managing editor Aseem Kishore wrote that “[MAC address filtering] really provides no extra security and can actually make your WiFi network less secure.” Periodic MAC address monitoring is a sufficient precaution in most cases.
Closing Thoughts
As with any type of security, you need to balance protection with practicality — for most of us on home networks, the five simple steps above will offer sufficient protection against the most common WiFi intrusion attempts. However, if you’d like to delve more into network security and set up additional barriers, we’ll leave you with some other tips:
- Reducing broadcast range is one easy (albeit potentially inconvenient) way to enhance security — hackers have to be within range of your network to breach it. On dual-band routers, the 2.4 GHz band can pass through walls and other obstructions more easily than 5 GHz, meaning that it extends beyond the property line of many homes. Disabling 2.4 GHz in your router settings will limit how far your network spreads, but may also lead to dead zones in your house.
- Disable remote management or SSH access. These features create a web gateway for remote login to the router, and provide one more avenue for hackers to attack. Thankfully, most routers have this feature disabled by default.
- Disable WPS. This press-to-connect “easy button” makes it more convenient to connect new devices to your router, but it’s also notoriously easy to crack the PIN, allowing hackers to completely circumvent your WiFi password. Many newer routers have lockouts to prevent continuous “brute force” WPS PIN attempts, but it’s safer to simply turn off this feature or buy a router that doesn’t support it.
- Disable WiFi when it’s not needed. This is the most extreme measure you can take, but the only one that guarantees the network can’t be hacked wirelessly. Some routers (such as Synology) offer the ability to turn WiFi on and off at scheduled times, so you can shut it down while you’re at work, asleep, or out of town.
For an in-depth checklist of router and WiFi network security measures, refer to RouterSecurity.org. However, keep in mind that many of the tips there are increasingly technical and bring a higher degree of hassle than the measures we discussed above.