If you’ve ever gotten locked out of your car, home, or office building, you’ll no doubt be familiar with the feelings of frustration and helplessness as you try in vain to get back in. It’s maddening to be unable to access your own belongings, and embarrassing to pay out of pocket for an expensive locksmith service or spare set of keys. Now imagine the added frustration if you weren’t locked out due to your own negligence — instead, a masked malicious individual forcefully kicked you out, then stood just inside the door, taunting you and demanding a ransom. In the digital world, this is known as a ransomware attack.

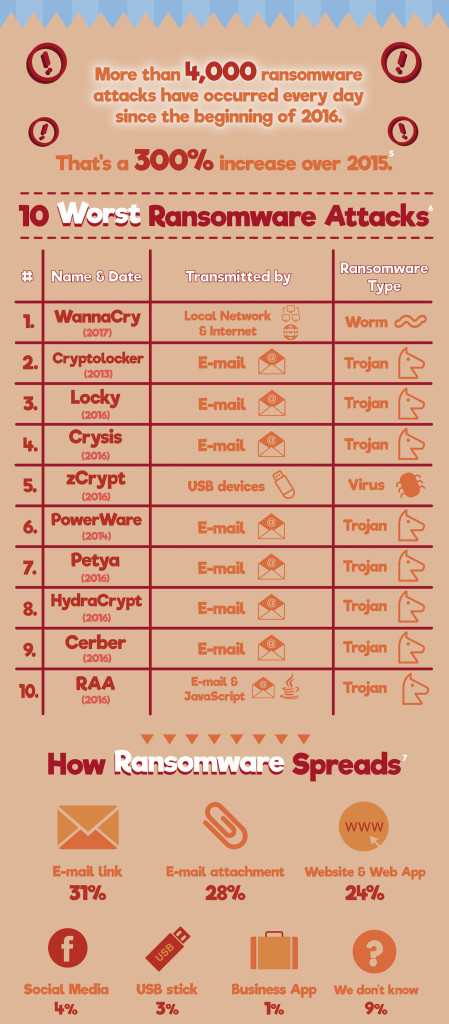
Ransomware is a growing threat, and this comes as no surprise to security professionals — it’s an effective method for unscrupulous cyber-criminals to make a quick buck. These attackers gain access to your computer through a compromised web link, email attachment, or even a USB thumb drive. Once the ransomware payload is unleashed, many or all of the files on your electronic device are locked and encrypted, and a message with ransom details is displayed on-screen.
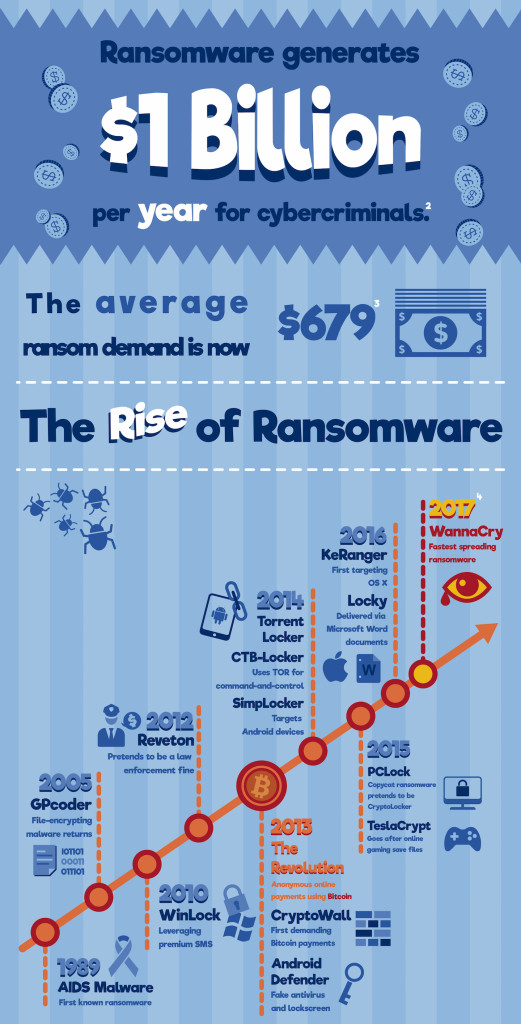
Usually, the anonymous attackers demand payment through BitCoin or another difficult-to-trace currency, and promise to restore your data only if you comply with their demands within a limited time frame. But you never know if they’re telling the truth — they’re already breaking numerous laws and holding your files hostage.
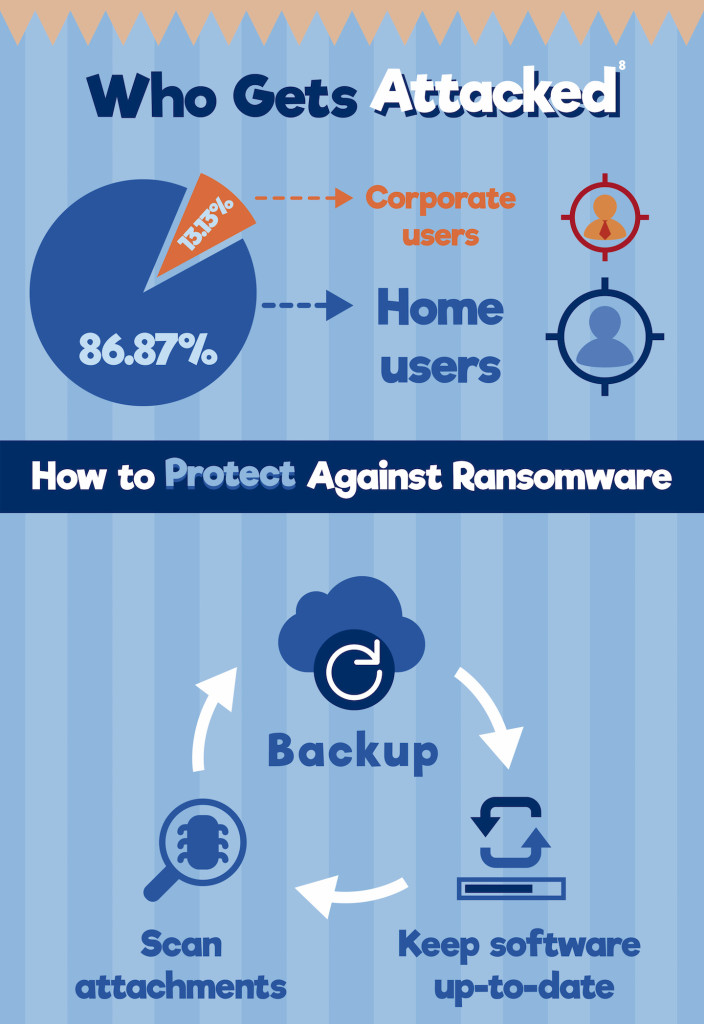
The following infographic from online data backup service BackBlaze.com provides more information on ransomware attacks and how they spread. Click here to download a full-size version.
Take the last section with a grain of salt, since it’s unsurprising that a cloud backup service provider would highly recommend cloud backup as a preventative measure against ransomware. However, it’s true that the best way to prepare for a ransomware attack is to backup your data early, often, and off-site. Directly-connected local backups such as external hard drives will likely be infected if they’re plugged into your device at the time of the attack, so you may want to keep them unplugged when they’re not in use. For more information, refer to our previous article on Surviving a Digital Apocalypse Through Backups.