In This Article
How difficult is it to find your phone number online? For most of us, the answer is “not very,” despite our best efforts. There are countless places where your phone number might be shared, whether it’s due to your own actions or those of a third party. Maybe you posted your number alongside a for-sale ad in an online marketplace, your spouse shared it in a community group on social media, or your boss emailed it to someone without your knowledge. Perhaps you signed up for a customer loyalty program at a store, and that store sold your name and number to make a quick buck. Maybe it was leaked in one of the countless data breaches that we hear about almost every day now. No matter the reason, phone numbers have become a key target for cybercriminals who carry out verification code scams.
What is a Verification Code Scam?
Two-factor authentication, or 2FA, has become an increasingly popular method of adding security to online accounts. The most common form of two-factor authentication involves sending a text message to your phone number with a verification code that must be used to take an action (e.g. reset a password, create an account, or allow a new device to log into an existing account). Everyone knows not to give out their passwords to strangers, but not all are as conscious of how 2FA codes work. Verification code scams involve convincing users to share those codes so criminals can take malicious actions, sometimes without requiring an additional password.
Now, you might be thinking, “That’s ridiculous! I would never give a verification code to a stranger.” That may be true — if you’re even a little security-conscious, you’ll know never to give out a verification code that you receive. Many verification code text messages also include a message that says “Don’t share this code with anyone.” But all of this can be overcome by a smooth-talking criminal who understands social engineering. (If that’s not a term you’re familiar with, read our article Social Engineering: 5 Manipulation Techniques.)
Even if you wouldn’t fall for this trap, your family members and friends might. That’s why it’s essential to share this knowledge with those who are less tech-savvy and more easily victimized.
How Do Verification Code Scams Work?
There are many ways cybercriminals convince victims to hand over their verification codes. For context, let’s look at a real-life example that has been circulating lately: the Google Voice scam.
Imagine you’ve listed an old iPad for sale online. As most people do, you enter your phone number so potential buyers can contact you. You receive the following message: “Hi, I’m interested in the iPad you’re selling. If it’s still available, I can send you the money through PayPal, but first I want to make sure you’re not a scammer. I’ve had too many close calls and I don’t want to get ripped off.” The message continues, “I’m going to use Google verification to prove that you’re a real person. You’ll get a text with a six-digit code from Google, so just let me know the verification code so I can prove you’re not a bot. Thanks!”
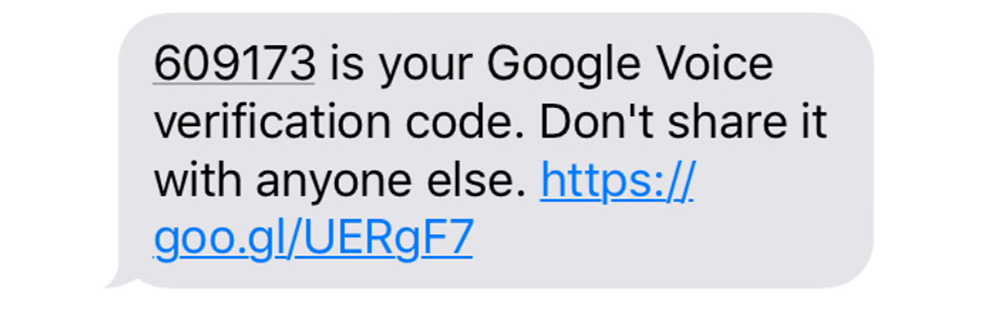
You then receive a code from Google that looks like this:
If you’re even a little skeptical, alarm bells should be going off in your head by now. Unfortunately, many people — often children or the elderly — don’t know better.
If the victim hands over the code to the criminal in this example, it’s used to set up a new Google Voice account with the victim’s phone number. That allows the scammer, who is usually overseas, to use the new Google Voice number to scam other victims (or to sell the number to other malicious groups). If authorities investigate, they’ll find the victim’s number linked to the scammer’s Google Voice account.
Here’s a guide explaining how to reclaim your number if you fall victim to the Google Voice scam.
Above: Security consultant and former Army Cyber Warfare Officer Rich Malewicz shared this example of a verification code scam in action. Even if it seems obvious to you, many people still fall for these brazen attacks.
Other possible verification code scams might be seeking access to accounts whose username and password data have previously been leaked. When a criminal already has access to the username and password, a 2FA code is usually the final key to taking over an account.
Now, maybe you’re not falling for the nice guy approach — that’s good. But there are other ways attackers convince victims to give up these codes. Fear is another common tool to convince victims to share a verification code. For example, a criminal might send an official-looking text that says, “ALERT: a new device has accessed your Amazon account near Shenzhen, China. A six-digit emergency verification code has been sent to this number. Reply immediately with the code to recover your account.” Uninformed users might panic and comply without realizing that this fraudulent message isn’t protecting their account from an attack — it IS the attack.
Methods to Avoid Verification Code Scams
The obvious answer is to do what most verification messages say: treat every verification code like a password, and never tell them to anyone. But there’s more to it than that.
Since SMS/text-message-based authentication is the most common method, it’s also the most common target for criminals. It’s a good idea to set up one of the other 2FA verification methods, either as a backup or your primary method. Authenticator-app-based (a.k.a. Time-Based One Time Password, or TOTP) verification tends to be more secure since its codes expire in as little as 30 seconds — probably not enough time for an attacker to use it, even if you were foolish enough to share it. Google Authenticator is a good example of this type of app.

For the extremely security-conscious, Google even offers an option to create a physical security key for 2-factor authentication. This requires you to insert a pre-programmed key, such as the Titan Security Key pictured above, into the USB port on your device to serve as your 2FA verification code. Unless someone steals the key, they won’t be able to access your account.
We also highly recommend creating one-time-use backup verification codes, which can be printed out or written down and saved in a secure location (e.g. inside a safe). If your primary 2FA method becomes inaccessible — for example, you lose or break your phone — these backup codes allow you to verify your identity.
If you suddenly receive an unexpected verification code that appears legitimate, it’s probably a good idea to go change your password immediately for that site, since it may be a sign that someone already has your username and password. Here are some tips on how to create a secure password.





