In This Article
Society’s use of the Internet has exploded over the last 20 years, and there’s no indication of it slowing down. As cyber technology grows, so do the vulnerabilities associated with these advances. According to the Center for Strategic and International Studies (CSIS), the global cost of cyber crime damages jumped from $445 billion in 2014 to $600 billion in 2017, and those numbers will undoubtedly continue to climb as criminals realize its potential for profit.
While U.S. cyber-security experts are some of the best in the world, other nations and non-state groups have equally talented hackers, many of which are looking for vulnerabilities in the United States’ digital defenses. While most Americans might suspect that their online bank accounts may be vulnerable to cyber criminals, what is surprisingly unknown to the general populace is the level of vulnerability in the nation’s electrical grid infrastructure.
If our power grid were to go black, conditions would be catastrophic. The truth, however, might allow us to sleep better at night. While many aspects of American society are open to cyber attacks, the national power grid may not be so easy to disrupt. To further explore the vulnerabilities of America’s electrical infrastructure, RECOIL OFFGRID asked some of the nation’s leading experts in cyber security to share their opinions on one looming issue: Can cyber-criminals actually cause a national blackout? Pablos Holman is a world-renowned hacker who has used his skills to further develop defense systems for both the federal government and private corporations. Dennis Santiago is a public policy analyst and the author of the Bank Monitor system currently used by financial institutions to assess security for a wide spectrum of U.S. banks. Finally, Patrick Miller is an independent security and regulatory advisor for industrial control systems in the energy, telecommunications, water, and financial arenas throughout the world.
Experts Discuss the Power Grid
RECOIL OFFGRID: How possible is it for a CT (cyber terrorism) attack to take down our electrical grid and what makes it vulnerable?
Pablos Holman: It’s impractical to take down a large portion of the power grid on a long-term basis. It’s a massively distributed infrastructure made of up thousands of power plants and stations throughout the nation. There’s a risk in having a “homogenous system,” meaning that if they were all the same, one exposed vulnerability would make the entire system vulnerable. The nation’s power grid is not a “homogenous system,” so it doesn’t run on the same power network throughout the country. The likelihood of taking down the entire system is very improbable.
Dennis Santiago: The power grid in the United States is mostly privatized and based on old technology. The control systems to manage the grid are several generations behind in relation to cyber security, especially compared to the sophistication of hackers today. There’s a disparity between what the hacker can do and what the defender can do throughout the system. Until that gap is closed, our power grid control systems are vulnerable to a crafty hacker. The most vulnerable portions of the grid today are external connections and weak passwords. In the past, we wanted maximum access and let human beings design passwords that are generally weak. Once a talented hacker is in the system, they basically could have their “run of the shop.”
Patrick Miller: It’s not physically possible to take down the entire power grid in North America, and it’s designed to be that way well before there were cyber attacks. The grid is broken up into three main pieces (East, West, and Texas grids) to ensure that the entire system doesn’t go down. One of the key components of the separation is called a “phase shifter,” which controls the pressure coming in or going out of the pipe so back pressure does not build up. Because of this, the phase shifter separates and moves the connection out of phase, so there is no physical way for the entire grid to go down.
People have said that Russia and China are already hacked into the grid. Is this true, and if so, how can their intrusion be blocked?
PH: Certainly Russian hackers are doing what they can to get into our system, and they do that opportunistically. They automate their attacks and try to take over as many computers as they can until you have a large network of victim computers that can be controlled remotely. Russia has a long history of meddling with elections, so it would be naïve of Americans to believe that they wouldn’t try during this last election. In the same way, it would be naïve of us to believe that they, or other competitive nations, wouldn’t be attempting to hack into our system and discover vulnerabilities.
DS: The single most successful hacking mission in history was actually perpetrated by the United States of America, who launched the Stuxnet cyber attack on the Iranian nuclear centrifuges in 2007. It was a massive success that set Iran’s nuclear program back several years. But when you do something like that, you also educate people how to counter-attack because they’ll study it in the aftermath. The Russians have a key interest in maintaining parity with the United States in such matters. As naturally expected, they’ll have probed into that technology as well. The Russians probe into our technology and systems all the time, but they mostly want to see what they can get away with. This way, they can boast about it and position themselves against the United States.
The Chinese are a bit different, because their hacking mindset is built on the exact opposite model of the United States. In the United States, people tend to distrust the government, whereas citizens in China are hyper-patriotic to their government. If something negative were to be said about China, then you have a multitude of Chinese college students who would immediately start to hack into American computer systems. Hacking has almost become an intramural game around the world to attempt to see if you can outsmart another’s cyber security defenses.
PM: I can’t say that it’s not true, but I haven’t seen any evidence that it is true. They are both very skilled and very competent countries when it comes to hacking. There is definitely motivation for them to be inside the grid. I would say that it’s probable and that their capabilities do exist, but evidence of them hacking into our nation’s power grid has yet to be shown, at least not maliciously.
What enables the nation’s infrastructure to withstand an attack currently, and what can be done to improve it for the future?
PH: The best thing that people and companies can do, without a doubt, is to perform system updates. Companies like Microsoft used to be wildly insecure with their systems until 14 years ago. About that time, they started to take security seriously and began to hire hackers and security experts to find vulnerabilities in their systems, and became very systematic with their efforts. Since then, they’ve taken a difficult task and have done it very well. Windows today is a very secure system overall, and Microsoft is very passionate about patching system loopholes when they exist. The same is true for companies like Cisco, Apple, and especially Google.
DS: One of the reasons that the nation’s power grid can withstand a massive cyber attack is that the U.S. grid system is privatized, and all power companies have different systems. It’s not a homogeneous system where everything has a common architecture across the power grid’s spectrum. The single most important act that can be done to improve the grid in the future is to make sure that everyone updates their passwords and changes them on a regular basis. It’s a very easy and innocuous thing to do, but it hardens your system right off the bat.
PM: The power grid is designed to experience widespread outages and continue to operate until it’s reconstructed. There are restoration plans in place in case an area goes dark. We’ve also got mutual assistance agreements in place with other utility companies to get crews and trucks to affected areas if needed. The whole thing is already designed to withstand massive-scale outages. Power companies approach massive power outages from an “all-hazards” approach, which makes much more sense than trying to pinpoint specific hazards to the system. To them, their mission is to respond and recover as quickly as possible, no matter the reason. Is it perfect from a cyber perspective? No. Is it vulnerable to a cyber attack, even scary vulnerable? Yes, there’s no doubt about that.
There’s this crazy mix of technology that dates back almost 70 years ago, and ranges to tomorrow’s micro-widgets like “smart dust,” which is edge-of-tomorrow technology. That diversity makes it exceedingly difficult for someone to attack the entire system with a virus or piece of malware that takes out everything. This is because you’re not going to get a Windows 7 virus to work on a 70-year-old remote terminal unit (RTU). The diversity of technology is a big player in the inability for a specific cyber attack to take out a very large spectrum, so your power outages are going to be regionalized at best.
What can families do to prepare for cyber security attacks, or attacks on the grid?
PH: From a security standpoint, the best thing may be to run iOS (an operating system used by Apple mobile devices). If you can, use an iPhone. iOS is very compartmentalized, so one app on your phone can’t access data from other apps on the same phone. It’s relatively secure. It’s also very difficult to load malicious code onto an iPhone. I’m not saying that it can’t be done or isn’t continually being attempted, but hacking into an iPhone, or sneaking a dangerous app into the App Store, is very difficult. As a result, iPhones or iPads are some of the most secure devices that you can get your hands on. Also, people often use the same passwords for different sites, and this makes them highly vulnerable to hackers stealing their information. When you can, always use “two-factor” identification. If you log into your account from a different computer, it will not only ask for your password, but require an additional login from your phone as well. This dramatically increases your security and can usually be found in the security preferences on the website itself.
DS: It depends on the duration of how long the grid is down for. For short periods of time, the remainder of the infrastructure is not going to go down along with the grid. You start getting into trouble when the grid is down longer, and the more critical things begin to disappear. Sewage processing, water pumping, medical services, and so on — these all take power. If the infrastructure that we take for granted begins to disappear, we’ll have to find ways to make up for their absence. Hospitals stop working, and the more advanced medical care that we’re accustomed to becomes non-existent. Issues such as water and sanitation that are required for survival, especially in an urban environment, become monumental tasks. One of the biggest things that we would lose for long-term survival is refrigeration. If you don’t have a refrigerator or any method of preserving food, the food supply chain begins to break down and starvation will increase.
PM: This is a challenging question because it depends on where you are. Preparing for a grid-down scenario depends on where you live because your power supply is contingent to what backup natural resources you may use for power. Anyone who doesn’t have those capabilities in their region is going to be out of power for a longer period of time.
What countries, terrorist organizations, and advocacy groups could have the power and resources to pull off such an attack?
PH: All the superpower nations, such as Russia and China, have this capability. We know that North Korea, Iran, and Syria also have the ability and a self-imposed motive. They all have access to extremely capable hackers, and if nothing else, look for vulnerabilities in our systems and infrastructure.
DS: The Iranians have a legitimate gripe to get back at us because we took down their nuclear program with the “Stuxnet” virus. You not only have to have the technological skills to perform an attack, but the organizational discipline to mount a proficient cyber attack as well. Nation states such as North Korea have both the technology and the discipline, but activist groups such as “Anonymous” lack the organizational skills to mount a large attack.
PM: What is often overlooked is organized crime. Some of the best hackers in the organized crime ring are not affiliated with anyone. They are hackers for hire, and often come from Brazil. Brazilian hacker skillsets are unmatched, and they’re some of the best hackers in the world. They have immense resources in Brazil and the freedom to do it without fear of consequences due to governmental turmoil. Rarely does China or Russia do the dirty work themselves. They often outsource that to third-party hackers or organized crime rings to give them plausible deniability. Everything that China and Russia does is for “the state,” whereas organized crime rings don’t care. They turn every social hacking construct on its head and break it in a heartbeat, because they think totally different than everyone else. There are no rules with these groups.
Would an attack on the grid be a massive effort, or could it be localized to a small group with a laptop?
PH: Localized attacks happen all the time. Last year, one of the biggest attacks was a Botnet virus called “Mirai,” written by a couple of 20-year-olds, that took over several hundred thousand webcams that were on the Internet. They then used that attack to bring down websites like PayPal and Netflix for 12 minutes! But an attack on the grid is a different level altogether.
DS: You’d have to have enough to overwhelm the other system, but you could possibly do a smaller attack with a laptop. I think that this will get much more interesting in the future when the technology turns more robotic, then one person can leverage a bunch of robots and essentially create an army to perform cyber attacks.
PM: From a cyber attack perspective, it would take an unimaginable amount of coordination, reconnaissance, and resources to take out an entire section of the national power grid. That kind of effort is likely to be picked up by someone in national security somewhere along the way. I think that the potential for something like that is small. It would be regionalized at best, or maybe a city like Chicago. It more than likely would be a power distribution center that’s hit. They may take out a large generator to stop power flow to an area, but the generators in the surrounding areas would just pick up that loss of power flow. The grid is built with multiple paths to protect against disruptions of power within the system. I’ll never say it’s impossible, but it’s very improbable.
What motivations would such a group have for such an action?
PH: You have some very disgruntled, disaffected youth in a marginalized society. Historically, their only tools were to start riots, social marches, and upheavals. There’s a lot of power in corporations and government, and many believe that “We the People” no longer have a voice the way we thought we did. When you look at cyber-activist groups like “Anonymous,” you’re looking at the next generation of social activists. Rather than use physical violence, they use the power of computer hacking. That turned out to be a modern tool for protests, and I don’t think that we’ve seen the end of it.
DS: There are state and non-state actors throughout the world that carry big grudges. Eco-terrorists would be a great example of a non-state group that could have a lot of capability to perform a targeted and regionalized attack on the grid. Often, these groups feel the need to assert resistance against the United States because they feel like we’re picking on them or their cause. Also, when other countries are being pressured diplomatically or with sanctions, they begin to explore options, such as cyber attacks, to retaliate in their own way.
PM: There are no new motivations today than there were since the dawn of humans. There are religious, economic, and geo-political motivations. These nations and groups hate what we stand for and in their minds, these reasons are all valid.
What are the immediate and far-reaching implications of a cyber attack?
PH: This is very sophisticated stuff and very poorly reported. If you want to get an accurate sense of a cyber attack, then the best-documented case is the use of “Stuxnet.” In this case, the U.S. government, in conjunction with the Israeli military, reportedly developed a computer virus that attacked Iran’s nuclear fuel enrichment plant and temporarily decimated their nuclear development ability. If you think about it, we used a computer virus to destroy a factory halfway around the world! That’s a very sophisticated, very targeted act of cyber warfare that we engaged in a handful of years ago. The “Stuxnet Virus” almost certainly not the biggest cyber attack that’s been used. It’s only the biggest attack that’s ever been made public. Since then, the use of cyber warfare as a method of attack has only escalated in the world.
DS: If one were to succeed in a massive cyber attack, it would stab at that population’s assumptions of survival. It will most definitely be a shock to both the power grid and societal systems. People will go through the entire spectrum of emotions, such as fear, anger, and overreaction. This will most likely be the most dangerous situation in a grid-down scenario. As a nation, we could launch a military strike against another nation and potentially start a war under “perceived” threats that may or may not be real.
PM: If any of the smaller groups attack any part of the electrical system, it will probably be viewed as an annoyance. But if it’s an all-out attack, then it’s seen as an act of war and the stakes are immensely high. The response to something like that would start off as significant global sanctions, and quickly escalate into deploying military forces. If Russia or North Korea would use a cyber attack to take out Houston or New York City’s grid for a month, we would likely have warships in their harbor overnight. This is massive defense response. It’s a life and death situation.
In the Shadows
Cyber attacks, also known as Computer Network Attacks (CNAs), are operations to disrupt, deny, degrade, or destroy information resident in computers and computer networks, or the computers and networks themselves. It may be waged against industries, infrastructures, telecommunications, political spheres of influence, global economic forces, or even against entire countries.
A well-planned cyber attack may include:
- Password sniffing
- Identity theft, fraud, extortion
- Malware, phishing, spamming, spoofing, spyware, Trojans and viruses
- Instant messaging abuse
- System infiltration
- Breach of access
- Denial-of-service and distributed denial-of-service attacks
- Private and public web browser exploits
- Intellectual property theft
Stuxnet: A Cyber Weapon for a New Age
The Stuxnet virus attack was a computer worm whose origins remain obscure — security experts believe it was launched through a joint effort between the United States and Israel. It was delivered via an infected USB flash drive, and adversely affected Iran’s nuclear enrichment efforts in 2010, setting their nuclear program back several years. The success of Stuxnet reveals that cyber-warfare is the future of war amongst not only the world’s superpowers, but rogue nations and activist groups as well. The revelation of Stuxnet further opens the gate to building cyber-defenses throughout the world, much like the nuclear arms race during the Cold War.
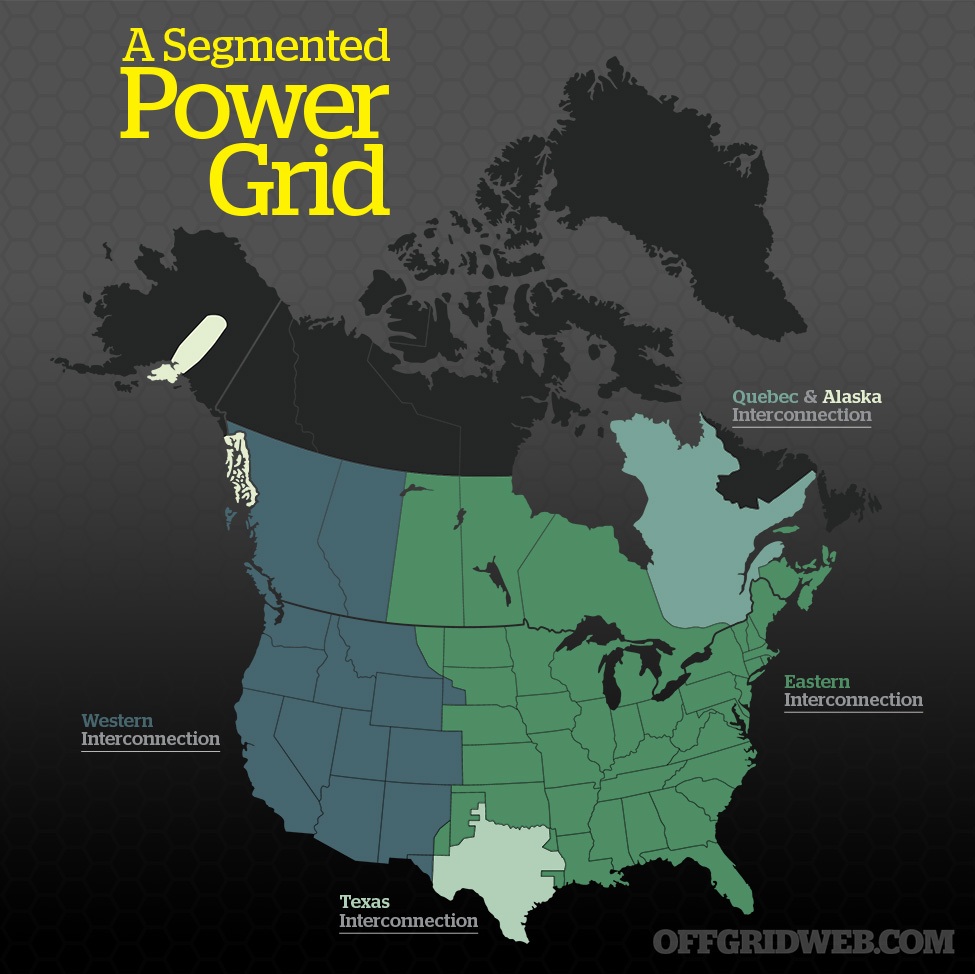
Infographic: Power Grid Segments
The National Electrical Grid that powers the continental United States is divided into three main regions. The Eastern Interconnection and the Western Interconnection are the largest grids in America. Three other regions include the Texas Interconnection, the Quebec Interconnection, as well as the Alaska Interconnection. Each region delivers 60 Hz of electrical power. The regions are not homogenous, and aren’t directly connected or synchronized to each other.
Western Interconnection
All of the electric utilities in the Western Interconnection are electrically tied together during normal system conditions and operate at a synchronized frequency of 60 Hz. The Western Interconnection stretches from Western Canada south to Baja California in Mexico, reaching eastward over the Rocky Mountains to the Great Plains.
Eastern Interconnection
The Eastern Interconnection reaches from Central Canada eastward to the Atlantic coast, south to Florida, and back west to the foot of the Rocky Mountains.
Texas Interconnection
The Texas Interconnection covers most of the state of Texas.
Quebec & Alaska Interconnection
While smaller in size, both the Quebec and Alaska Interconnections make up the remainder of the North American power grid.
Conclusion
Life in America has become more complicated, especially as the nation’s infrastructure becomes more dependent on technology. As the use of technology increases, so does our vulnerability to those who want to exploit our private lives for personal gain. While many citizens remain open to cyber hacking on a daily basis, we can be reassured that the lifeblood of America, its power grid, still remains relatively secure from the malicious acts of cyber terrorism and those who commit such offenses. We should always take steps to prepare ourselves and our families for the worst, but it’s also important to consider the evidence that executing a massive cyber blackout may be based more on fiction than fact — at least for now.
[meetourpanel]
About the Author
Mark Linderman is the preparedness coordinator for the Wayne County Health Department where he has served for over 18 years. He instructs disaster preparedness and bioterrorism courses for several universities, including Indiana and Arkansas State University. He also teaches crisis and emergency risk communication courses for the Centers for Disease Control and Prevention, and is considered a subject-matter expert in crisis/risk communications for Vantage Point Consulting, based in Indianapolis.
More From Issue 31
Don’t miss essential survival insights—sign up for Recoil Offgrid’s free newsletter today!
- Antibiotic Alternatives: Plants, Poultices, & Pet Meds
- Book Review: “Bushcraft” by Mors Kochanski
- Parental Preps Issue 31
- 360-Degree Illumination: Survival Lantern Buyer’s Guide
- How to Make a Family Disaster Plan
- Escape & Evasion Evaluation: SERE Kit Buyer’s Guide
- Freedom From Fallout: Is Nuclear War Still an Imminent Threat?
- Blackout Bulwark: How Vulnerable is the Power Grid to Cyber Terrorism?
- Mike Glover Spotlight – Redefining Survival
- Survival BB Guns: Backyard Shooting Gallery
- Survival Spuds: Building Your Own Potato Patch
- Pocket Preps: Glass Breaker
- What If You’re Lost at Sea?
- Gear Up Issue 31
Read articles from the next issue of Recoil Offgrid: Issue 32
Read articles from the previous issue of Recoil Offgrid: Issue 30
Check out our other publications on the web: Recoil | Gun Digest | Blade | RecoilTV | RECOILtv (YouTube)
Editor’s Note: This article has been modified from its original version for the web.